Hackathons are a fun environment and there’s a time and place for jokes during one. Who hasn’t made a joke about being sleep deprived or stinky after one? That said, jokes about bombs or hurting people in general are not ok. Ever.
This weekend at Hack the North, we had an incident where two students made a joke in poor taste about building a bomb. Their comments were inspired by recent events with Ahmed Mohamed and his clock.
We were alerted to the presence of the post by other participants who saw it and felt unsafe. We acted in accordance of the Major League Hacking incident response procedure and our official code of conduct. We worked with the event organizers to locate the individuals and alerted the relevant authorities and school administration.
In this case, it was clearly a joke in poor taste and they didn’t actually build a bomb. However, because of the nature of the incident, we expelled them from the event immediately and covered their expenses to get home. Both participants were aware of the severity of the situation and departed from the event on good terms.
As hackers, we deeply sympathize with Ahmed and are supportive of his creative exploration. In fact, we’re working with another Major League Hacking event to get him to his first hackathon. We hope he attends! That said, this is not an example of creativity being misunderstood. This is an example of a bad joke that went too far. If anything, this incident set Ahmed’s cause back by being insensitive to real issue at hand.
If you have questions, please find Swift at Hack the North or email us at incidents@mlh.io. We’re happy to discuss it.
Happy Hacking,
— Swift
Edit: September 19th, 2015 @ 7:24pm ET
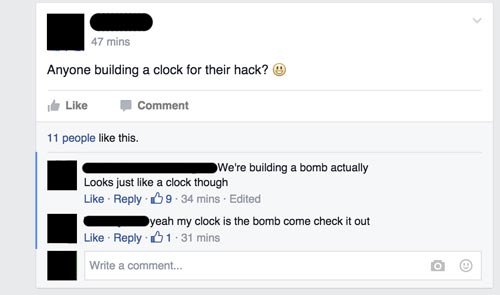
Much of the confusion around this situation is related to the missing original comment. The intent of the Facebook administrators was to delete the entire post, not just one of the comments. Below is a redacted screenshot of the original thread.
The proximity of the comments and the relationship between the participants led us to treated both comments as a single incident.
Edit: September 20th, 2015 @ 7:06pm ET
Cross-posted from a thread on Facebook:
“Hey folks, we completely understand that people want more insight into the process here. We have an official incident response policy inspired by resources provided by the Ada Institute, Pycon, and other leaders in the field. In any situation where we receive a report, this policy is followed explicitly. One of the first steps in an incident is to make the organizers aware of the situation. We then go on to gather information from everyone involved so that we may make an informed decision. After consulting those involved and the organizers, we react with a measured response. Depending on the severity of the situation, this may include contacting local authorities and/or the school administration. If an attendee ever disagrees with a decision made, they may, of course, appeal through the same reporting mechanisms and a similar process follows.
At Hack the North, volunteers approached us after receiving a report from an attendee who felt unsafe after viewing the posts on Facebook. The Hack the North Security Coordinator, amongst other Hack the North staff were immediately involved. We then found the students who made the report and the individuals who made the Facebook comments. Upon finding them and notifying them of the situation, we immediately contacted the school’s provided security firm. In consult with the security firm and the Hack the North Security Coordinator a decision was reached to remove the attendees from the event, due to the nature of the situation. We worked with the security firm to do so and then paid for their ticket home. Following this we informed the university’s on-site employee and local police.
In this incident the Hack the North organization was involved throughout. In this and all other incidents we respond to every attendee’s safety and wellbeing is our primary concern.”
Edit: September 22nd, 2015 @ 9:53am ET
Hack the North posted their official response, which can be found at http://hackthenorth.com/hackthenorth-response.pdf